Why is Facial Authentication Preferred Over Other Security Checks?
Facial authentication is rapidly becoming the gold standard for physical access control. There are several benefits to utilizing this form of identity verification. For simplicity, we will cover the top five reasons why organizations are making the switch to this method of advanced security.
#1 – Reduces Lost, Stolen, or Shared Credentials
Alternatives to biometric security include proximity cards, passcodes, or the traditional physical keys.
Proximity cards use a radio frequency (RFID) chip that transmits an employee’s credentials to the scanner which permits or denies access, based on the user’s credentials. One of the downfalls to proximity cards is the risk of them being lost, stolen, or shared. Furthermore, proximity cards require RFID chips, which currently are not available due to supply chain issues. It is believed this issue will resolve after the COVID-19 pandemic.
Passcodes are often used at access points to try and thwart unauthorized individuals from gaining access. This is likely one of the least secure methods of security for a few reasons. First, if employees can choose their passcode, they are likely to use one they use elsewhere, decreasing the actual security of the passcode. Second, if they do not choose the passcode and it’s the same for all authorized individuals, the security is again decreasing in integrity. Third, inputting passcodes each time access is needed, does not promote frictionless security. Finally, there is no identity verification of the person inputting the access code into the system, just whether or not the codes are correct.
#2 – Increased Security Protocols

Using facial authentication as a means for access control increases the integrity of the physical infrastructure. By using one’s face as their credentials it becomes essentially spoof proof. Meaning, that you cannot beg, borrow, or steal someone else’s credentials to gain access into a restricted area.
As with any other security controls, there is a threat of tailgating. Tailgating is when an unauthorized individual gains access to a restricted area by following an authorized party. However, unlike other security controls, facial authentication tools offer real-time alerts for such behavior. When tailgating occurs, the proper staff is notified to address the concern immediately to reduce the threat of a potential breach.
#3 – Frictionless, Hands-Free Approach

Unlike other biometric security solutions, facial authentication offers a hands-free approach that enables frictionless access control.
There is no need to scan a fingerprint, enter a passcode, or pause for retina or iris scanning. Facial authentication enables employees to continue their daily operations and access abilities by simply looking at the scanning device and in seconds their verification will be identified.
Furthermore, due to COVID-19, many organizations have begun reducing the physical touch-points throughout an organization. They do not want employees touching the same fingerprint readers or passcode panels. Facial authentication offers a hands-free, germs-free approach to security.
#4 – Easy Installation, Use, & Integration
Not all facial authentication tools are equal; however, there are a select few that make the entire process incredibly easy and effective. When considering different facial authentication tools, it will be important to understand the onboarding process, updating process, and how it will integrate with existing systems.
First, how easy is it to install? Will it require an entire tech team for the installation and setup? Or, perhaps it will be as simple as installing the hardware and doing a control scan of each employee? From there, there are facial authentication tools that have artificial intelligence and machine learning-enabled to account for changes in a person’s appearance. This could be weight loss, a change in hairstyle, glasses, or aging. Finally, It would be unrealistic to assume an organization has no access controls enabled. Therefore, it will be important to understand whether or not the facial authentication technology will replace the existing solution, or be added on as a multi-layer approach. If it is the latter, is that an option for the technology you are considering?
#5 – Multi-Factor Authentication
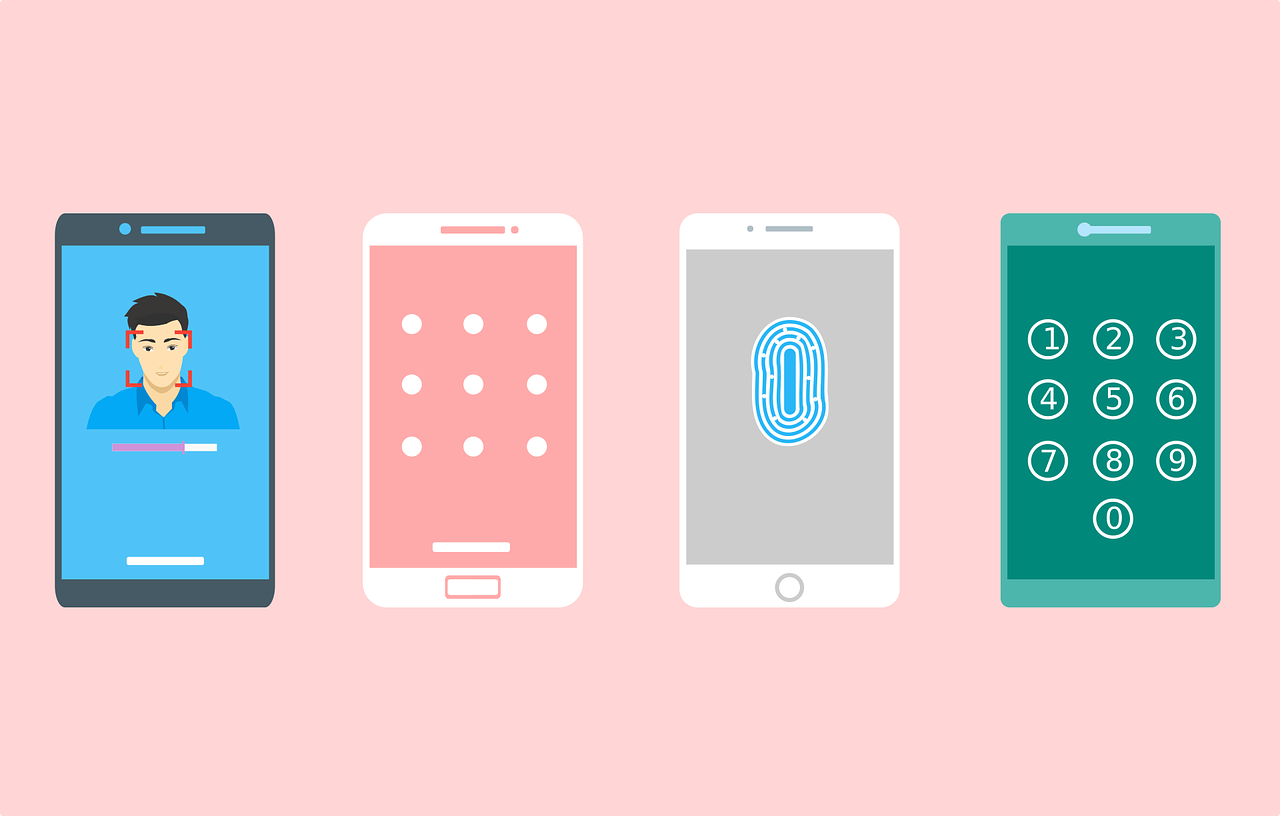
In most cases, using facial authentication as a multi-factor layer to your security stack is entirely within the realm of possibility. Not only does it promote advanced security, but also allows for an organization to keep its existing security layers in place without having to rip and replace the entire infrastructure.
This approach also eliminates the security risks associated with other methods of access control, like fobs or proximity cards, and passcodes.
There are an array of reasons why facial authentication technologies are the preferred method of access security. Overall, they promote better security, offer a frictionless-access control environment, and reduce the spread of germs across employees. The adoption of hands-free security methods was quickly adopted pre-pandemic. However, due to the increase in employee safety measures, it is being introduced as a method of safety for organizations to get employees back into their physical workspaces as quickly, and safely as possible.